The internet is vast and constantly expanding, with new websites and services popping up every day. However, there’s a part of the internet that remains shrouded in mystery and is often the subject of rumors and myths – the Dark Web.
Definition of the Dark Web
The Dark Web is a portion of the internet that is not indexed by traditional search engines such as Google, Bing, or Yahoo. This means that it’s not accessible through a normal web browser like Google Chrome or Mozilla Firefox. Instead, you need to use specific software or tools to access the Dark Web, which is why it remains hidden from the majority of internet users.
The Dark Web is often associated with illegal activities, such as the sale of illegal goods, services, and information, but it’s important to note that not all of the content on the Dark Web is illegal. Some people use the Dark Web to maintain privacy and security while communicating or accessing information.
Importance of the Dark Web World
Although the Dark Web has a reputation for being a hub of illegal activity, it’s important to understand that it can also be used for good. For example, journalists and activists in countries with restrictive governments use the Dark Web to communicate safely and securely without fear of censorship or retaliation.
Additionally, understanding the Dark Web can help you stay safe online. For instance, knowledge of the Dark Web can help you spot scams and phishing attempts, as well as protect your personal information.
What is TOR?

TOR (The Onion Router) is a free, open-source software that enables users to access the Dark Web. It works by routing your internet traffic through a series of servers, making it difficult for anyone to track your online activities or determine your location.
It is a widely used tool for online privacy and security, with over 2 million daily users and a presence in over 30 languages. A study conducted by the University of Cambridge estimated that around 7% of TOR users access the Dark Web, highlighting its popularity as a tool for accessing restricted content. In 2018, a report by Freedom House emphasized the significance of TOR as a tool for online freedom of speech and privacy.
The TOR network is made up of over 7,000 relays, with over 2,000 active at any given time, and is managed by the TOR Project, a non-profit organization dedicated to the development of the software. A 2021 study by the GlobalWebIndex found that TOR usage had risen by 20% in the previous two years, with the software being most popular among tech-savvy, younger users.
How Does Tor Work?
The software was originally developed by the U.S. Navy as a way to protect government communications, but it has since been made available to the public.
When you use TOR, your internet traffic is encrypted and sent through a series of servers, each of which strips away a layer of encryption. This creates multiple layers of encryption, hence the name “The Onion Router.” By the time your internet traffic reaches its final destination, it’s encrypted and impossible to trace back to you.
To access the Dark Web with TOR, you need to download and install the software, and then use it to connect to a Dark Web website. It’s important to note that while TOR provides a high degree of privacy and security, it’s not completely foolproof. You should still be cautious and take steps to protect your privacy and security while using the Dark Web.
How TOR Protects Your Privacy
One of the primary benefits of using TOR is that it protects your privacy and security. By routing your internet traffic through multiple servers, TOR makes it difficult for anyone to track your online activities or determine your location. Additionally, the encryption used by TOR ensures that your data is secure and protected.
When you use TOR, your internet traffic is encrypted and sent through a series of servers, each of which strips away a layer of encryption. By the time your internet traffic reaches its final destination, it’s encrypted and impossible to trace back to you. This makes it an ideal tool for people who value privacy and security online.
How TOR Works with the Dark Web
The Dark Web is a portion of the internet that is not indexed by traditional search engines, and it requires specific software or tools to access. TOR is one of the most popular tools for accessing the Dark Web.
To access the Dark Web with TOR, you need to download and install the software, and then use it to connect to a Dark Web website. The encryption used by TOR ensures that your data is secure, safe and protected from prying eyes, even while accessing the Dark Web.
Common Misconceptions about TOR

Despite its popularity, TOR is often the subject of rumors and misconceptions. Some people believe that TOR is only used by criminals or that it’s illegal to use. However, these claims are false. TOR is a legitimate tool that is used by journalists, activists, and others who value privacy and security online.
Another common misconception is that TOR is completely anonymous and that there’s no way to trace your online activities. While it’s true that TOR provides a high degree of privacy and security, it’s not completely foolproof. For example, if you access the Dark Web and engage in illegal activities, law enforcement may still be able to track you down.
How to Set Up and Configure TOR
This is a crucial step for anyone seeking to protect their online privacy and security. We will walk you through the process of downloading and installing the TOR browser, configuring it for maximum privacy, and providing best practices for safe browsing with TOR.
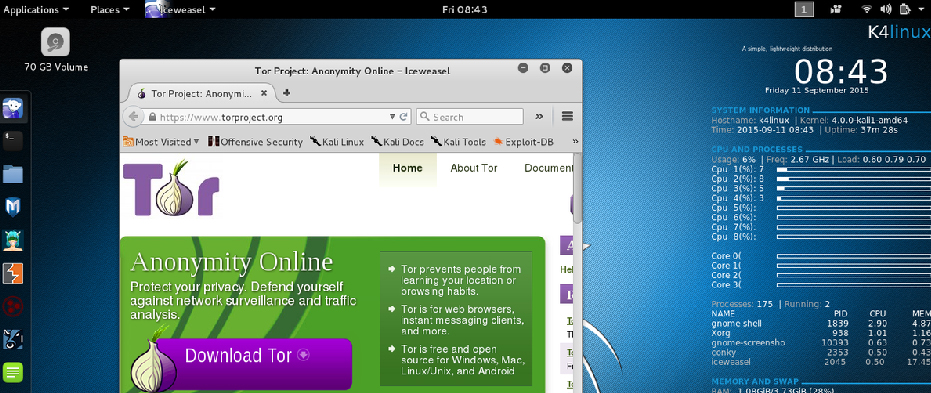
Downloading and Installing TOR
The first step to set up and configure TOR is to download and install it on your device. TOR, or The Onion Router.
To download and install TOR, follow these steps:
- Visit the TOR Project website at https://torproject.org/
- Click on the “Download” button on the website
- Select the version of TOR that is compatible with your device’s operating system (e.g., Windows, macOS, Linux, etc.)
- Follow the instructions provided to install TOR on your device.
After you have successfully installed TOR, you can start using it to browse the internet anonymously.
Configuring TOR for Maximum Privacy
By default, TOR provides a basic level of privacy and security, but you can further enhance your anonymity and security by configuring the settings to meet your specific needs.
Here are some steps you can take to configure TOR for maximum privacy:
- Change the default settings:
- Open the TOR Browser and click on the three horizontal lines in the top-right corner.
- Select “Options” and then “Privacy & Security”.
- Make sure the following options are selected: “Block third-party trackers”, “Block dangerous and deceptive content”, and “Warn me when websites try to install add-ons”.
- Enable HTTPS Everywhere:
- Click on the three horizontal lines in the top-right corner of the TOR Browser.
- Select “Add-ons”.
- Search for the HTTPS Everywhere add-on and install it.
- This add-on encrypts your communication with most websites, which provides an added layer of security.
- Use a New Identity:
- Click on the three horizontal lines in the top-right corner of the TOR Browser.
- Select “New Identity”.
- This will create a new circuit and provide you with a new IP address, making it more difficult for anyone to track your activities on the internet.
- Avoid using the same TOR circuit for multiple activities:
- When using TOR, it’s best to use separate TOR circuits for different activities.
- This makes it more difficult for anyone to track your activities on the internet.
- Use a VPN in conjunction with TOR:
- Using a VPN (Virtual Private Network) in conjunction with TOR can provide an added layer of privacy and security.
- A VPN encrypts all internet traffic between your device and the VPN server, and then the encrypted traffic is sent through the TOR network.
- However, it is important to choose a trustworthy VPN service, as some VPN services can compromise your privacy and security.
Best Practices for Safe Browsing with TOR

Certainly! Safe browsing is important for anyone who wants to protect their privacy and security online, and TOR can help with that. But it’s essential to follow some best practices to ensure that your browsing experience with TOR is as secure as possible. Here are some of the key things to consider:
- Use the Latest Version of TOR: Always ensure that you’re using the latest version of TOR, as older versions may have vulnerabilities that can be exploited by malicious actors.
- Avoid Logging into Sensitive Accounts: Don’t log into sensitive accounts, such as email or online banking, while using TOR. This is because even though TOR provides an extra layer of security, your login credentials could still be intercepted.
- Be Careful with Downloads: Be cautious about downloading files from unknown sources, particularly executable files with extensions like .exe or .dmg. These files could contain malware that could compromise your privacy and security.
- Disable JavaScript: By default, JavaScript is enabled in the TOR browser, which could potentially compromise your privacy. To ensure safe browsing, it’s recommended to disable JavaScript in the TOR browser settings.
- Use HTTPS Everywhere: TOR browser includes the “HTTPS Everywhere” plugin, which automatically encrypts your connection to websites that support HTTPS. This adds an extra layer of security to your browsing experience with TOR.
- Avoid Peer-to-Peer File Sharing: Peer-to-peer file sharing networks can compromise your privacy and security while using TOR. Avoid using them while using TOR.
Finding Reliable Dark Web Websites
One of the biggest challenges of accessing the Dark Web is finding reliable websites. The Dark Web is known for hosting illegal and unethical activities, so it’s important to be cautious when searching for sites to visit. Some popular Dark Web marketplaces, such as the now-defunct Silk Road, have been taken down by law enforcement, and others have been discovered to be scams.
To find reliable Dark Web websites, you can start by searching for lists of trusted sites on forums or blogs dedicated to the Dark Web. You can also ask for recommendations from people you trust who have experience with the Dark Web. However, it’s important to remember that even the most reliable websites can still have security vulnerabilities, so you should always be cautious and take necessary precautions when browsing the Dark Web.
Understanding Dark Web URLs and Addresses
The Dark Web operates on a different system of addresses than the regular web. Instead of using familiar domains like .com or .org, Dark Web sites use .onion addresses. These addresses can only be accessed using the TOR browser, which is specifically designed to allow anonymous browsing of the Dark Web.
Dark Web URLs and addresses can be difficult to remember, so it’s recommended to keep a list of the sites you want to visit in a secure place, such as an encrypted note-taking app or a password-protected document.
How to Access and Browse the Dark Web Safely
To access the Dark Web safely, you’ll need to download and install the TOR browser, which you can get from the official TOR website. Once you have the TOR browser installed, you can use it to access Dark Web websites by entering their .onion addresses.
When browsing the Dark Web, it’s important to take steps to protect your identity and security. This includes:
- Using a VPN to encrypt your internet connection and hide your IP address
- Avoiding downloading any files or clicking on links from untrusted sources
- Being cautious of phishing scams, where attackers try to trick you into entering sensitive information, such as passwords or credit card numbers
- Keeping your computer and software up-to-date to prevent vulnerabilities from being exploited.
Common Risks and Threats on the Dark Web

Despite its anonymous nature, the Dark Web is still a dangerous place. And users are at risk of being targeted by cybercriminals, hackers, and other malicious actors. Some of the most common risks and threats on the Dark Web include:
- Malware: Dark Web sites are a common source of malware, which can infect your computer and steal sensitive information, such as passwords and financial information.
- Scams: There are many scams on the Dark Web, including fake marketplaces, phishing sites, and fake services. Always be cautious and do your research before making a transaction or entering any personal information.
- Extortion: Attackers may use information obtained from the Dark Web to extort money or sensitive information from individuals and businesses.
- Legal Consequences: Accessing and participating in illegal activities on the Dark Web can result in serious legal consequences, even if you are doing so anonymously.
Accessing the Dark Web requires a great deal of caution and awareness of the potential risks. While it can be a source of information and services that are not available on the regular web. It’s important to understand the dangers and take necessary precautions to stay safe.
Staying Safe on the Dark Web

I) Identifying and Avoiding Scams and Frauds
Scams and frauds are a common occurrence on the Dark Web. So it’s important to be vigilant and take steps to protect yourself. Here are some tips for identifying and avoiding scams and frauds on the Dark Web.
II) Look for Signs of Legitimacy
One of the first things to look for when assessing the legitimacy of a Dark Web website is the design. Legitimate websites will usually have a professional-looking design, a privacy policy, and contact information that you can use to reach the website’s owner.
III) Beware of Offers That Seem Too Good to Be True
Another common tactic used by scammers is to lure people in with attractive offers or deals that are too good to be true. If an offer seems too good to be true, it probably is. So, be wary of any offers that seem suspicious. And always do your due diligence before making any transactions on the Dark Web.
IV) Don’t Trust Unsolicited Messages
Be cautious of unsolicited messages or emails, especially those that ask for personal information or money. Scammers often use these tactics to trick people into giving away their sensitive information or money.
V) How to Respond to a Cyber-Attack
Cyber-attacks can happen at any time, so it’s important to know how to respond if you suspect that your device has been compromised. Here are some steps to follow if you suspect that you’ve been the victim of a cyber-attack on the Dark Web.
VI) Disconnect Your Device
If you suspect that your device has been compromised, disconnect it from the internet as soon as possible. This will help prevent the attacker from gaining further access to your device and information.
VII) Run a Security Scan
Use security software to scan your device for malware or other security threats. This will help you identify any security issues and take steps to remove them.
VIII) Change Your Passwords
Change all of your passwords, especially those for any financial accounts or sensitive information. This will help prevent the attacker from accessing your accounts and information.
IX) Seek Professional Help
If you’re not sure how to respond to a cyber-attack, seek help from a professional who specializes in cybersecurity. They can help you assess the extent of the damage and take steps to secure your device and information.
Final Thoughts
The Tor network and the dark web are complex and multifaceted phenomena that are essential to understanding in today’s digital age. While the dark web can be used for criminal activities, it also offers privacy and protection for whistleblowers, investigative journalists, and individuals seeking freedom of speech. The risks associated with accessing the dark web, such as exposure to malicious content. And threats to personal privacy, must be carefully weighed against its benefits.
The responsibility for ensuring the safe. And ethical use of the dark web lies with both governments and internet service providers. Accessing the dark web safely requires following best practices, using the right tools, and being aware of the potential dangers. The future of the dark web is uncertain, but its impact on our digital lives will likely continue to evolve.